
Admin By Request Launches New Datacenter POP in Singapore
Singapore is a strategic market and the opening of this datacenter underscores our commitment to providing secure, localized solutions for our customers.
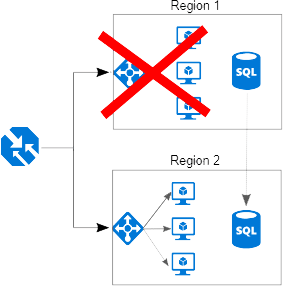
We use Microsoft Azure SQL to store your data in two regions - USA and Europe. We use two locations in each region using SQL replication to make sure your service stays up and running in case of Microsoft Azure outages. If you are based anywhere outside Europe, your data is stored in the USA in the states of Virginia and Washington. If you are based in Europe, your data is stored in the Netherlands and Ireland. All our web servers are located in the same four locations for optimal performance for you. None of your data exists outside of these designated regions.
Yes. If you want us to store your data in the opposite region to where you are based, please let us know by the time you license.
Data is real-time geo replicated between the two locations in your region to ensure backup, fail-over and disaster recovery. Microsoft backs up Azure SQL and guarantees an Azure SQL restore is possible from any minute of the day, within the last 30 days. We also do cold storage backup in case of a complete, irrecoverable Microsoft Azure failure on both locations in a region.
We keep your auditlog data for 12 months by default. You can change the data retention period in your settings from a minimum of 3 months to a maximum of 5 years.
The service level agreement for Azure SQL is 99.99%. In case of a failure, geo replication will automatically fail-over to the secondary location.
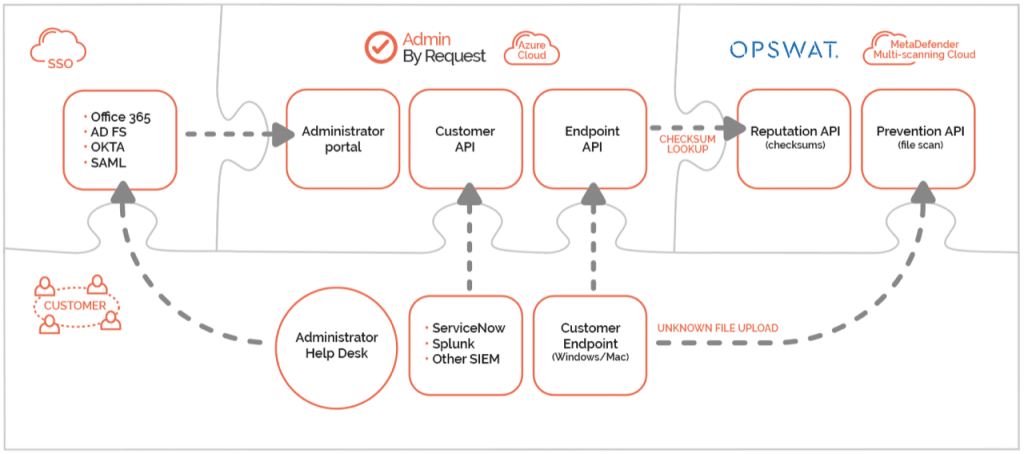
The following communications take place:
We use Azure SQL transparent data encryption for all data at rest to ensure no unauthorized access to data is possible.
The data communication between the client software and our servers uses TLS 1.2 encryption. The load balancer IP depends on your region:
Furthermore, the raw data is also encrypted using a 256-bit encryption to protect against Man-in-the-middle attacks by a person who has physical access to a client.
The inventory collects:
NOTE: In case of GDPR concerns, you have the ability to disable the collection of user name, account name, email address and phone number in the Settings menu after login. You can also disable the entire inventory if you prefer.
The client software collects this information from a domain controller for domain computers:
The traffic is marginal and only refreshed every 4 hours. You can monitor the traffic on an endpoint by running the ADInsight SysInternals tool.
When a user has completed an App Elevation or an Admin Session, the client collects:
If the Reason screen is used, email address and phone number are also collected, as entered by the user in the pop-up window. You can disable collection of user name, email address and phone number in the Privacy menu in Settings in the portal.
In a support situation, one of our support engineers might ask the end user to invoke the About screen, click the Connectivity tab and ask the end user to click the “Submit diagnostics data” link. This will send trivial system data to us to understand the history of the endpoint software. If the end user clicks the link and confirms, the client submits:
This data cannot be extracted by us without the user clicking the link and is kept for up to a week. Note that an end user cannot create a support ticket, only portal administrators can.
The client software for domain joined computers works exactly the same off of your LAN as it does on your LAN. This is possible because the clients cache an encrypted copy of domain groups’ names and OU name of the computer and the logged-on user, to be able to determine sub settings both online and offline. If your computers are Azure AD joined, a similar group’s cache is kept for performance reasons. If your computers are stand-alone, no data is cached.
Only the appointed Risk Owner and/or Asset Owner has access to the production environment (maximum 2 persons). Please refer to our GDPR Data Processing Agreement for more information.
We have strict security policies in place for all our employees. Please refer to the technical and organizational measures outlined in our Data Processing Agreement, Annex III.
Because we use VirusTotal Monitor (VT monitor). VirusTotal (www.virustotal.com) is owned by Google and offers scanning of files from 70 AntiVirus vendors including CrowdStrike, Sophos, McAfee, MalwareBytes, BitDefender, Symantec, TrendMicro, Kasparsky, F-Secure, FireEye, Microsoft, Webroot, Avast, Fortinet and Acronis. Our files can simply not be deployed without passing the scan of all 70 engines.
Please review our Terms & Conditions for using Admin By Request. Terms & Conditions along with the GDPR Data Processing Agreement are the two agreements in effect between you and us for you to be able to use Admin By Request.
Admin By Request is developed by FastTrack Software, which is a European company, and we must therefore abide to the EU General Data Protection Regulation - GDPR in short. To comply with Article 28 in the General Data Protection Regulation, any European company must provide a Data Processing Agreement (DPA) between themselves and any European customer. The agreement applies to all customers around the world, which means all customers reap the benefits of the GDPR requirements observed by us. The overall purpose of Article 28 to describe internal procedures relating to security, availability and privacy when managing customer data, with the main objective being customer transparency. Click the link to see the agreement.
ISO/IEC 27001 is an information security standard - part of the ISO/IEC 27000 family of standards. It is published by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC) under the joint ISO and IEC subcommittee. ISO/IEC 27001 specifies a management system that outlines requirements and is intended to bring information security under management control. Organizations that meet the requirements may be certified by an accredited certification body following successful completion of an audit. FastTrack Software is ISO 27001 certified. The documentation can be found in the Trust Center.
Service Organization Control 2, known as SOC 2, is developed by the American Institute of CPAs (AICPA) and defines the criteria for managing customer data based on five "trust service principles": Security, Availability, Processing integrity, Confidentiality & Privacy. SOC 2 and GDPR Data Processing Agreements are very similar and they both address the same procedures. The key difference is that a GDPR Data Processing Agreement is based on the right to audit by the customer, whereas SOC 2 is a certification by a trusted third party. We are currently in the process of obtaining a SOC 2, which is expected to complete in Q4 2023.
Cyber Essentials is the UK Government’s answer to a safer internet space for organisations of all sizes, across all sectors. Developed and operated by the National Cyber Security Centre (NCSC), Cyber Essentials is considered the best first step to a more secure network, protecting you from 80% of the most basic cyber security breaches. FastTrack Software is fully certified to UK Cyber Essentials. Please refer to the Trust Center for certificate of proof.
At the time of licensing, you will receive a main login. With this login, you can create multiple logins with limited access, such as access for an auditor or a manager. A login also grants rights to see the same data in the mobile app. For all users, you can enable two factor authentication and single sign-on. If you received an NFR license for a proof-of-concept project, and you later choose to license, this tenant instance will automatically roll on to become your commercially licensed tenant.
We support single sign-on (SSO) for Office 365, Azure AD, ADFS, Okta and any SAML 2.0 identity provider. We recommend that you set up single sign-on because this ensures that you terminate access to the portal when employees leave the company. Refer to this page for technical setup of SSO.
We use Azure web servers in multiple continents in order to make sure we provide great performance anywhere in the world and that the portal is always up and running.
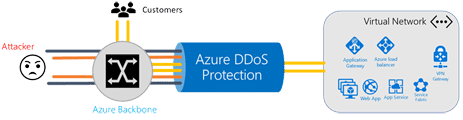
The portal is protected from Distributed Denial of Service by Azure DDos protection. Refer to the document below for more information:
Our web servers are located in the same Azure Availability Set in each continent. An Azure Availability Set is a guarantee that Microsoft will not take web servers down for maintenance at the same time. Microsoft guarantees a 99.95% up time in each continent in this set up:
Singapore is a strategic market and the opening of this datacenter underscores our commitment to providing secure, localized solutions for our customers.
BYOD is convenient, but risky. Discover 8 major security threats and how to protect sensitive data on employee-owned devices without hurting productivity.
One email. No clicks. Full data breach. EchoLeak shows how AI assistants like Microsoft Copilot can become dangerous tools in the wrong hands.