In the war on COVID-19, security compliance is the un-named casualty
We’re three weeks into COVID-19 ‘Lockdown’ and the more online meetings I hold with our customers and suppliers, the more I realise that IT departments across the world have pulled off heroic, business saving tech-ops of ‘Dunkkirk-esk’ proportions.
In 1941, the British miraculously plucked their 338,000 strong Expeditionary Force off the beaches of northern France with a zillion little ships, in just eight days.
79 years later, IT staff command a flotilla of hastily assembled technologies to break through the COVID-19 lockdown blockade. The crews of MV Microsoft 365, HMS Zoom and SS-L VPN should all receive ‘distinguished service medals’ at the end of the ‘Cornoa conflict’.
With staff based at home, IT faces a constant battle to provide even bare bones of functionally to keep business operations above water. C-level kitchen conflabs are held to assess the collateral damage, yet there’s one casualty that is given neither official recognition nor solemn commemoration.
In the struggle for operational ‘buoyancy’, security compliance ‘ballast’ got hacked free and cast off.
One wonders how many times ‘COVID-19’ will crop up in future ISO 27K audits?
For every angry auditor, there’s a happy hacker
This is a predicament we suspect many businesses find themselves in today, caught in the barbed wire of the COVID-19 crisis. The consequence of wholesale compliance lapse primes an already highly explosive cocktail of domestic grade security mixed with a suddenly decentralised and disorientated workforce.
There can only be one beneficiary from such a situation. For hackers, COVID-19 sets up a turkey shoot of targets, and opens an unattended sweet shop of opportunity. A bogus, but expertly forged email advising of a newly available (or cancelled!) home delivery slot might be all that’s required for them to score a direct hit.
We at FastTrack Software recognise that due to the scale of upheaval the COVID-19 crisis has caused, many businesses right now are super stretched, and super vulnerable.
The purpose of this blog is to ‘throw you a rope’ by highlighting eight specific features contained within our Admin By Request solution that could help your business through this and potentially future COVID-19 lockdowns, so you can safely navigate the minefield of security compliance consequences.
Advancing the home
I was on a revealing call with a customer last week. Faced with a two-month lead time for new kit, I suggested he might have to hire a paleontologist to discover ‘Dino-dell laptops’ in peoples atics in order to get the entire office working from home. With an ironic laugh he admitted that he sent out an atic search party the previous week, anything that could run Windows 10 was dusted off and re-commissioned for the greater good!
Here’s the thing. Armed with Admin By Request, keeping a newly enlisted fleet of (perhaps less than ideal) home worker systems protected, productive and fully compliant is not as big a deal as you think.
Read on to see eight reasons why…..
1. Rapid reaction force: Built for AzureAD & Intune

You are probably thinking that, after successfully completing the titanic task of ‘home-boarding’ your entire workforce, torpedoing them all with a Privilege Access Management system might end up being ‘The Longest Day’ for you, and a ‘Bridge Too Far’ for your colleagues.
Think again! Admin By Request, being a product from us automation experts at FastTrack Software, has ease of deployment designed in. Whether you are on Active Directory, Azure Active Directory, or basic stand-alone PCs, all three scenarios are supported within the same infrastructure free SaaS based configuration. To say the solution can be deployed and activated within minutes is no exaggeration. The zero-config installer MSI measures just a miniscule 3.5MB in size.
Thanks to Windows 10 and its native Azure AD join feature, it’s particularly easy to use Microsoft Intune to roll out Admin By Request to remote users. It’s simply a case of uploading the MSI (downloaded from your Admin By Request portal account), to Intune as a ‘Line of business’ application. Then it’s simply the case of assigning it to whatever Azure AD groups you need to roll Admin By Request out to. For more information on how to do this, see our Azure AD documentation pages.
2. PCs on parade: The system Inventory
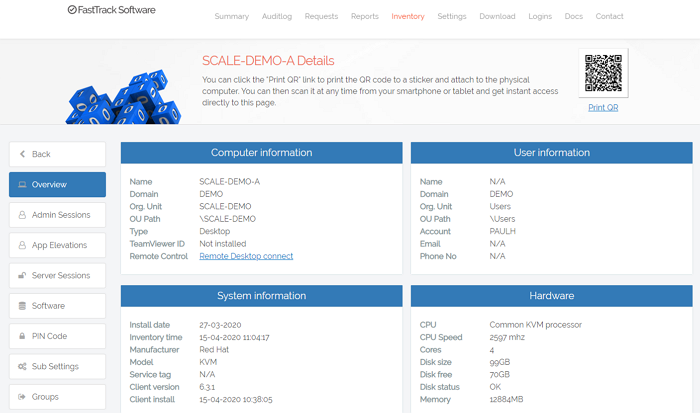
Shortly after automated deployment, you will immediately start to notice Admin By Request clients popping up in the Inventory section of the portal. Don’t assume this is simply a list of Admin By Request agent deployments, no, this is far more. Admin By Request ships out of the box with a full blown client inventory system. Such functionality, in times like these, is extremely useful.
Not only does the inventory system report back security related information such as user accounts with Local Admin rights and AD group membership, there’s a lot more that will come in handy.
QR codes are automatically generated and can help you check in/out systems for your asset management as you move them to and from staff homes.
You can look up TeamViewer IDs, list each PCs full software load (with versions and install time) and discover hardware information including service tags / serial numbers. All of this is searchable and filterable in the portal, and the mobile app too.
Whether it’s determining whether a home PC has enough grunt to run Photoshop, or to track down and errant laptop via Geo-IP lookup, the inventory system that ships with Admin By Request is included as standard, simple to use, and seriously useful.
3. Admin rights recon: Learning Mode
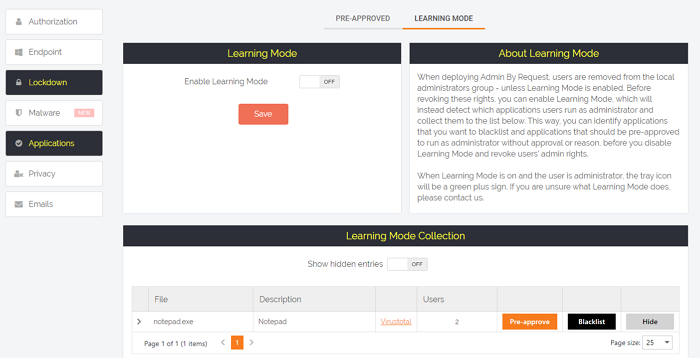
Whether you are lucky enough to grab new stock, re-imaging old kit, or even asking staff to use their own PCs at home, it’s likely that many users will, as default, find themselves with Local Admin rights. Security compliance requires these rights be revoked, but might doing that in an indiscriminate fashion cause more problems with existing software that requires admin rights? It sounds a bit silly but for staff using home PCs to work on, the house CCTV system, or even software that configures the robot lawn mover might need local admin to function, so cutting their rights, might end up preventing them from trimming their lawn!
Learning Mode is exactly feature for situations like this where Local Admin rights are ‘in play’, but the ramifications of removing them may not be fully understood. Being purely a ‘reconnaissance’ feature, learning mode enables IT staff to deploy Admin By Request without any ‘implications’ of rights revocation on the client.
Because Admin By Request is still running in the background, all elevation tasks are logged, and this means there can be a full and clear understanding of what revoking rights will do. Some user accounts may need exclusions, and some forgotten or unknown (but valid) applications may need whitelisting.
Of course it’s true also that users might be elevating some applications when they do not, and should not need to. Learning mode will show these up so you can give the user guidance and apply a corrective action.
All of this means that when you finally hit the switch to revoke Local Admin rights, it all happens in a seamless and non-dramatic fashion. Any scrambled eggs will remain firmly on your breakfast plate, and not all over your face.
4. Getting the troops in order: Sub settings
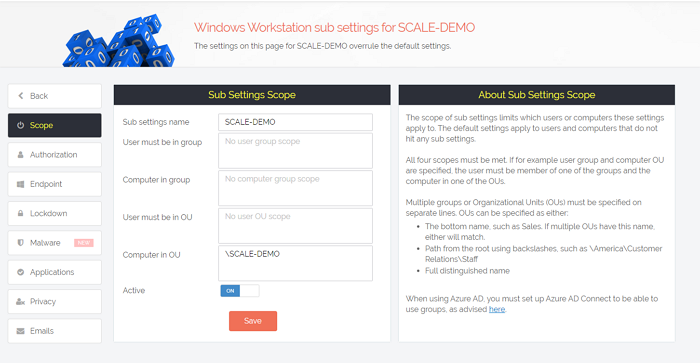
One of the learnings from the use of learning mode, is that some home workers will be found to require different elevation and revocation setups than others. This is easily configured using our sub setting system, which enables one to replicate ‘global’ settings but ‘scope’ them on AD or Azure AD groups so they can be tweaked and tuned to specific OU or group members.
You can configure rights revocation, allow auto apps elevation, set different elevation modes and workflows, all based on membership of a particular sub setting.
You can also ‘scope’ portal / mobile ‘app. users to sub settings, so that for example, the department head of ‘Development’ only gets to view and manage configurations, rights and view audits from his or her department. This is an essential feature to enable local admin rights departmental delegation, especially the case now where need to release the pressure on IT helpdesks who already have their hands full dealing with other COVID-19 lockdown challenges.
5. The business end: Four elevation modes

Once you have deployed, learnt, and created groups of settings, home based users are now able to perform just in time, ad-hoc elevations based on one of our four elevation modes:
PIN only.
Issue One Time PIN codes for instant full session elevation for ad hoc use. Ideal for those that do not need / not permitted to submit their own, on demand per-app of full session elevation requires.
Pre-Approval.
IT departments can set up ‘whitelists’ of applications which all or groups of staff can elevate in isolated fashion without any requirement for manual approval or extra malware checks.
‘Run As Admin’ mode.
With this mode, users can request elevation of applications not found in ‘pre-approval’ with the additional protection of pre-elevation OPSWAT MetaDefender malware check. Like pre-approval Run As Admin mode elevates just the requested process rather than give the user system wide elevation.
Full Session mode.
This is our time limited, fully audited and malware protected session elevation mode. Ideally suited to users such as developers that need more freedom to elevate multiple applications at a time.
All modes can be used together and can be assigned to an unlimited number of settings groups.
6. Defensive insurance: Integrated OPSWAT MetaDefender
Our latest feature, available in Admin By Request 6.3, is our ground-breaking real time and in-line OPSWAT MetaDefender malware engine integration. Users working in the home setting typically run low grade, domestic class network security, and might be operating PCs loaded with non-standard, out of date, or even no AntiVirus software at all. On installation, Admin By Request instantly hardens all privilege elevation activities by enforcing a real time malware check on any elevated files, against MetaDefenders impressive multi-engine malware / file reputation solution.
User elevation requests that come back as likely malware are automatically quarantined and trigger alerts to portal administrators to perform swift investigation.
So no matter what one A/V solution your users tell you they have working (if one at all), with Admin By Request you know that for file elevations, your back is covered by a suite of 20 engines including CrowdStrike Falcon ML, McAfee, Bitdefender and Kaspersky.
7. Out on manoeuvres: Mobile App
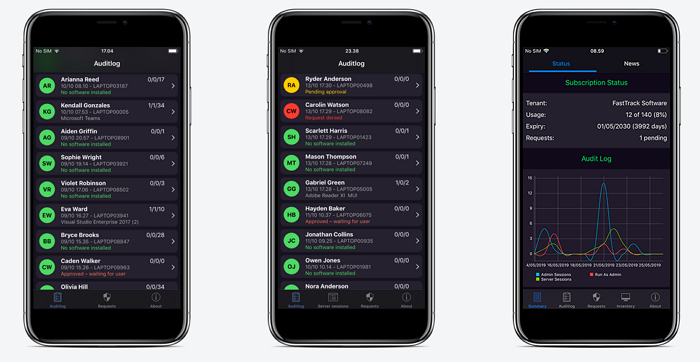
The staff are all at home, and likely so are you, along with the rest of your IT team. With children at home and your partner having to get the weekly shop alone, you might find yourself managing Nintendo Switch tantrums and staff Local Admin rights elevation requests at the same time.
Admin By Request’s mobile app (supports both iPhone and Android devices) enables portal administrators to effortlessly review and approve requests, as well as review the inventory and issue PIN codes, all from their mobile devices.
So in the home lockdown environment, whatever situation you find yourself in and whoever happens to be using your PC, all you need to do in order to review and process admin rights requests, is reach into your pocket.
8. “Masterly retreat is in itself a victory”: Local User and AAD user restore on uninstall
Finally, you can deploy Admin By Request in a hurry to home PCs and revoke rights, secure in the knowledge that when COVID-19 is done and you no longer need to cover these systems, all the Local and AAD user rights are put right back how they were before Admin By Request was installed.
Summary
From initial deployment, all the way through to decommissioning, Admin By Request is the ideal tool to rapidly implement Local Admin rights management in demanding and diverse situations. It’s quite simply the easiest way to maintain compliances and harden security whilst enhancing staff productivity in these unprecedented times.
At FastTrack Software, our mission with Admin By Request is to enable your business not just to survive the challenge of COVID-19, but hopefully come out the other side with a workforce that is more resilient, more productive, and better able to dynamically adopt to any potential future COVID ‘counter-attacks’ to come.