Cyber Essentials
Throughout my 25 years as an IT professional, I have acquired reputation for being perhaps the most pessimistic person on the planet. Far from this being an utterly negative quality; I am regularly told by customers that my attitude of assuming the worst is a stand out speciality! For me, the expectation that something will go wrong, is the best way to ensure that it does not, and be totally prepared for it if it does.
So it was most satisfying for me to discover that none other than the UK Government GCHQ share a similar mindset when it comes to IT security. Here in the UK, our CGHQ / NCSC (National Cyber Security Centre) have done some truly excellent work in the development of business centric security frameworks such as Cyber Essentials. They have published lots of easy to read, plain English material and at the same time given them ‘teeth’ in that non-compliant businesses get locked out of public sector contracts.
Crucially, they are not only publishing guidelines on best practice for Malware infection prevention, but also for ‘damage limitation’ when ‘successful’ infection occurs. Yes, you read that correctly, they specifically state when, not if. If you don’t believe me, why not take a few minutes to read through GCHQ’s guidance on ‘Preventing Lateral Movement’.
You do not have to get too far in before they make a sobering assumption:
“You should assume that an attacker with sufficient time and resources will eventually be successful.”
When I read this, it brought a tear to my eye!
Of course, it should always be the case that we focus our minds and invest in preventative solutions, but it would be foolish & irresponsible to think the worst could never happen.
Lateral Thinking….
High up on the list of CGHQs top means to protect your organisation from lateral movement POST attack are requirements to ‘Protect high privilege accounts’ and ‘Apply the principle of least privilege’.
As you would expect from GCHQ, the critical requirement is clearly defined:
“Using time-based privileged access can help reduce the impact of a leaked admin credential, especially as it will be audited every time the user requests or receives it. Identifying high-risk devices, services and users can help in planning granted privileges, ensuring that those with the highest risk have the lowest privileges.”
Admin By Request: Privilege Management For The Masses
Here at FastTrack Software, Admin By Request (affectionately abbreviated to ‘ABR’ by customers in a hurry) is our feature rich, affordable & hyper ‘thin’ Privilege Management Solution.
Is it perfectly designed to help any size of organisation comply with the privilege management aspects of security frameworks such as Cyber Essentials:
- Initially deploy ABR in ‘Learning Mode’ to discover / detect the size of your privilege problem / risk without any disruptive changes in working practice
- Report privilege assessment to key company stakeholders to make them aware of potential issues / compliance problems in order to get top down buy in for the next step.
- Automated removal of all Local Admin rights companies wide from non-IT admin role staff
- Controlled time limited access to Local Administrator rights elevation on a session or per app level
- White-listing and blacklisting of applications
- Full auditing and inventory of PCs.
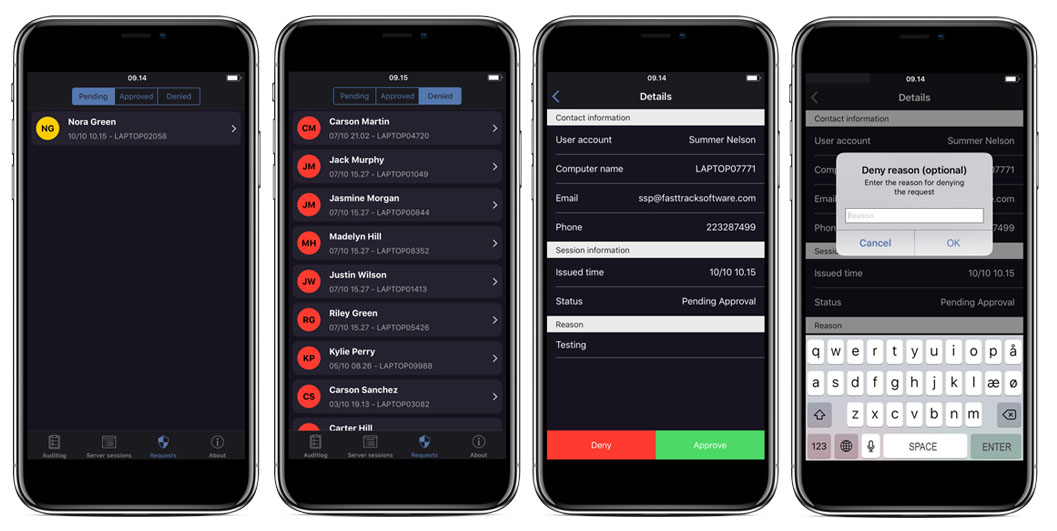
- Ability to manage via mobile app (iphone / Android)
- Of course you can do all of this with our Free Plan
Don’t Forget Your Servers!
With Admin By Request: Server Edition, you will always have to hand an easy to review audit of all server admin logon activity company wide. You will never have to give a 3rd party contractors / vendors temporary domain admin rights again for them to perform management or maintenance tasks. This satisfies another important Cyber Essential requirement of “Monitor user activity, particularly access to sensitive information and the use of privileged account actions” (Step 7 in NCSCs 10 steps for managing user privileges)
Infrastructure Free, Deploys In Seconds
Being a portal-based solution there is no additional infrastructure required for you to deploy ABR HOWEVER critically, our portal only handles settings and workflow aspects of the solution, so all the executable aspects of ABR happen on the client.
Remember, there is no sending of passwords or any security sensitive data to the portal, and what data is sent (most of which can be selectively disabled) is done so via HTTPS AES 256 and then within this another tunnel of AES 256, an additional layer of proprietary encryption.
Privilege Management: Tick!
So whether your business is going for Cyber Essentials, Cyber Essentials Plus (which involves being audited by an external IT security company) or an even more comprehensive certification such as ISO 27001, having our Admin By Request ‘green tick’ icon on your PC task bars throughout your organisation will result in another tick: next to the ‘privilege management’ section of your next security audit report!
Why not get started with the Free Plan today?
Credit: Many thanks to Jack Miller, Systems Admin @ pcspecialist – as the inspiration behind this blog post!












