For most of manufacturing history, factory floor systems and corporate IT networks didn’t talk to each other. Operational technology (the PLCs, SCADA systems, and industrial controllers that run production) lived in its own isolated world. If ransomware hit your office network, the machines kept running. That separation was the security model, and for a long time it worked well enough.
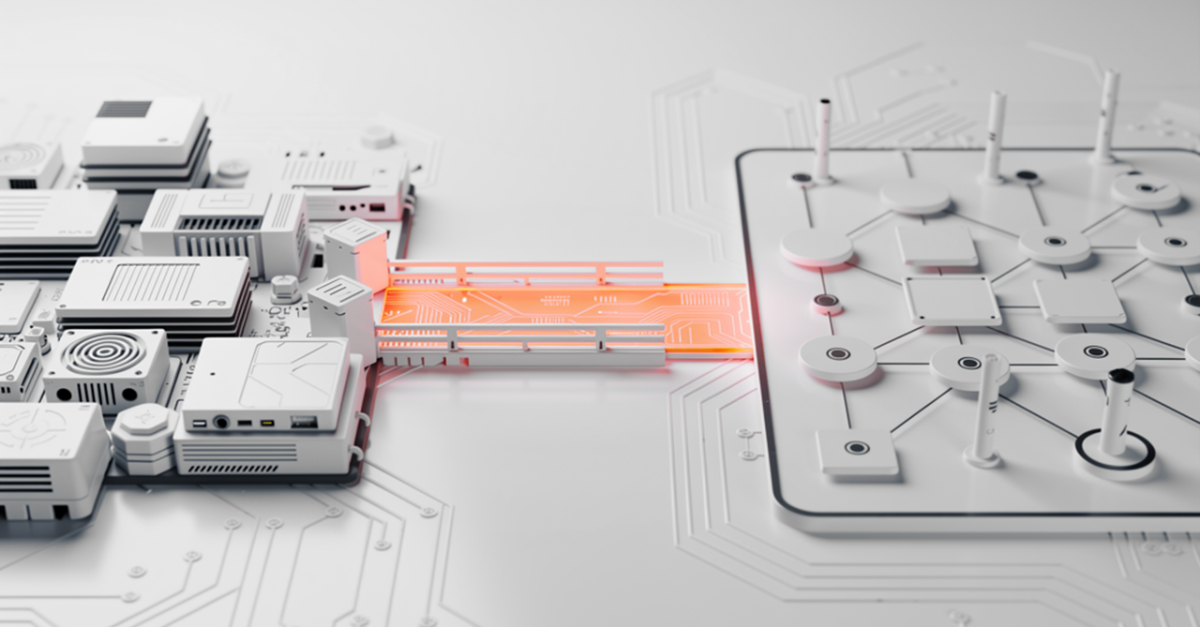
That world is largely gone. Manufacturers are connecting OT and IT to enable real-time production monitoring, remote diagnostics, vendor maintenance, and software updates pushed directly to industrial equipment. The efficiency gains are real. So are the security implications.
When OT and IT converge, the factory floor inherits all of IT’s vulnerabilities. A phishing email that compromises a corporate workstation can become a pathway to industrial control systems. A vendor connecting remotely to service a machine can become an entry point if that access isn’t properly controlled.
Ransomware attacks on manufacturers have surged, and production shutdowns are now a common outcome rather than a worst-case scenario. Securing those new connections without grinding operations to a halt is where most manufacturers struggle.
Why OT Security Is Its Own Beast
IT security thinking doesn’t always translate cleanly to OT environments. In IT, the classic security triad is Confidentiality, Integrity, and Availability, roughly in that order. In OT, availability comes first. A production line that’s down costs money by the minute, and security controls that risk causing downtime get pushed back against hard.
OT systems also have long lifecycles. It’s not unusual to find industrial controllers running software from 10 or 15 years ago, on hardware that was never designed with network connectivity in mind. Patching isn’t always possible, and even when it is, maintenance windows are tight and infrequent. On top of that, the people operating these systems aren’t IT staff. They have deep expertise in their equipment, but credential hygiene and network segmentation aren’t their concern. Controls that demand significant behavior change from them tend to fail in practice.
Any serious approach to OT security has to account for those constraints upfront, or it’ll run into them halfway through implementation instead.
Where the Real Exposure Is
The consequences also aren’t limited to production downtime. Manufacturers hold a lot of valuable intellectual property: process designs, formulations, product specs. An attacker who gets in quietly and exfiltrates that data can cause serious damage without ever touching a production system, and that kind of intrusion can go unnoticed for months. Most of that risk traces back to three recurring problems:
- Overprivileged accounts. When IT and OT converge, admin rights tend to proliferate. Engineers get broad access because they’ve always had it, IT staff get access to OT systems because someone needed to set them up, vendors get access because scoping it precisely felt like too much effort at the time. The result is a large number of accounts with more access than they need, and very little visibility into what those accounts are actually doing.
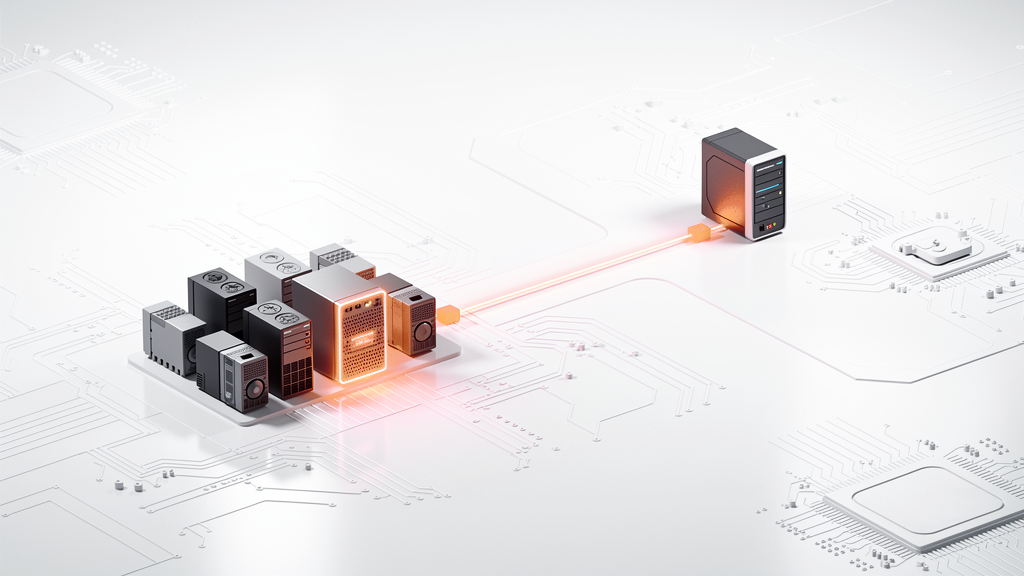
- Uncontrolled vendor access. Vendors typically connect via VPN with persistent credentials, access more systems than strictly necessary, and their sessions are rarely monitored or recorded. Supply chain attacks have become a leading vector across critical infrastructure, and manufacturing is no exception.
- Remote access tools set up in a hurry. Many manufacturers stood up remote access to OT systems fast during COVID-19, and the priority was getting it working. VPNs with shared credentials, RDP exposed to the internet, and remote support tools with no audit trail are common findings years later.
Getting Controls in Place Without Disrupting Operations
The most common mistake is trying to fix everything at once. A security initiative that causes production downtime or generates serious pushback from operations tends to stall, and then nothing gets done.
1. Start With Visibility
Deploying privilege management in a logging-only mode lets you see exactly what elevated tasks are being performed before you revoke anything. Audit existing remote access and vendor connections. That picture tells you what needs to be accommodated and builds the internal case for why changes are necessary.
2. Remove Permanent Admin Rights
Replacing them with just-in-time elevation means users and technicians request access when they need it, for specific tasks, and it’s automatically revoked when they’re done. For pre-approved routine tasks, that elevation can be fully automatic with no IT involvement. For sensitive or unusual requests, an approval workflow kicks in. Admin By Request EPM is built around exactly this: a technician who needs to push a firmware update or change a network configuration can do it through a self-service request, without a help desk ticket or waiting on IT staff. Access is logged, audited, and time-limited.
3. Get Vendor Access Under Control
What you want is access that’s scoped to the specific systems the vendor actually needs, granted on request, time-limited, and fully logged. When the session ends, the access is gone. Our Secure Remote Access solution handles this through a dedicated vendor portal where external users authenticate via SSO and connect to internal devices through their browser, with no additional software required and no visibility into anything outside their defined scope. Every session is logged and can be recorded.
4. Segment the Network
Even with good access controls, a flat network means an attacker who gets in can move laterally with few obstacles. OT systems should sit in a separate network zone from corporate IT, with firewall controls governing what traffic passes between them. The aim is ensuring lateral movement requires explicitly permitted paths rather than being unrestricted by default, without trying to recreate the strict air gap that characterized pre-convergence environments.

The Goal Is Security That Operations Can Live With
The manufacturers that get this right do it gradually and pragmatically. They start with visibility, address the highest-risk areas first, and build out controls in a way that respects how operations actually run. Pre-approval for routine elevated tasks means day-to-day work isn’t disrupted. Just-in-time vendor access means third parties can still do their jobs, just within clearly defined limits.
A security program that’s technically sound but operationally impractical will either get overridden or quietly abandoned. Getting operations and security teams aligned on the approach from the start, with controls that fit into existing workflows rather than cutting across them, is what makes the difference between a rollout that sticks and one that doesn’t.