Baited and Hooked: How Phishing Evolves to Outsmart Us
Discover how phishing has evolved with advanced tactics like clone phishing, BEC, and AI-driven scams. Learn crucial defense strategies to protect against these threats.
Discover how phishing has evolved with advanced tactics like clone phishing, BEC, and AI-driven scams. Learn crucial defense strategies to protect against these threats.
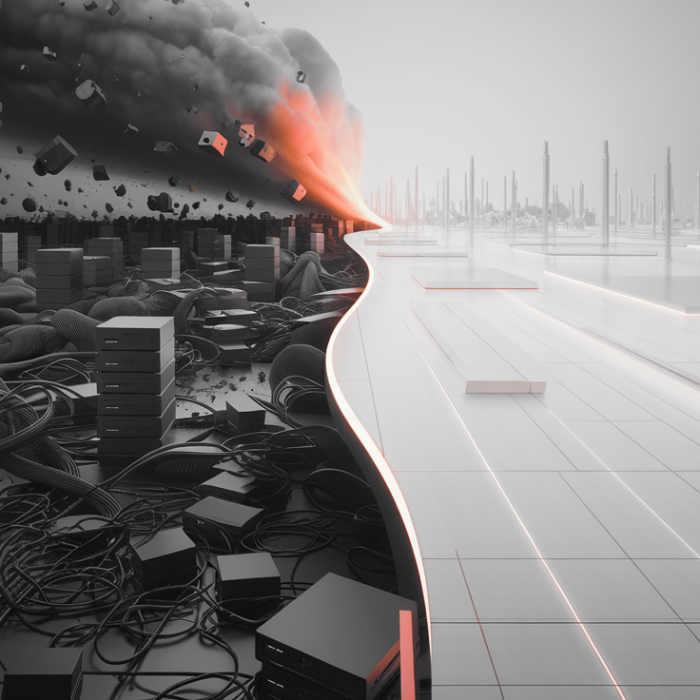
Explore the economic impact of the May 2024 ransomware attack on CDK Global, emphasizing the necessity of strong cybersecurity measures.
Complex networks aren’t a blocker for PAM. Admin By Request handles AD sprawl, proxy setups, and hybrid auth with zero disruption.
Replace insecure VPNs with zero trust vendor access. Admin By Request uses Cloudflare to provide just-in-time, browser-based access to internal systems.
Web browsers store sensitive data. Lock them down with hardening strategies to prevent infostealers from stealing passwords, tokens, and session cookies.

